
Kali Linux, known for its prowess in cybersecurity and ethical hacking, provides a powerful command-line tool called `netstat` for monitoring active network connections. This tool is indispensable for identifying potential security threats, troubleshooting network issues, and gaining insights into the network activities of your system.
In this article, we’ll delve into the world of `netstat` and explore how it can be used effectively in Kali Linux.
Understanding `netstat`
`Netstat`, short for “network statistics,” is a versatile command-line utility that reveals information about active network connections and routing tables on a Linux system. It is an essential tool for network administrators, security analysts, and anyone interested in understanding the network traffic on their system.
Here’s a breakdown of the key components of the `netstat` command and their significance:
- `-a`: This option instructs `netstat` to display both listening and non-listening sockets. Listening sockets are those actively accepting incoming network connections, while non-listening sockets represent established or pending connections.
- `-n`: When you use this flag, `netstat` shows numerical addresses instead of attempting to resolve them to symbolic hostnames, ports, or usernames. This can be especially useful when you need a quick overview of active connections without the delay of hostname resolution.
- `-t`: The `-t` flag narrows down the output to display only TCP (Transmission Control Protocol) connections. TCP is a connection-oriented protocol widely used for various network communication purposes, such as web browsing and file transfers.
- `-p`: This option reveals the process identifier (PID) and the associated program names for each socket. It allows you to pinpoint which processes are responsible for specific network connections.
Practical Usage
Let’s put this knowledge into practice. Suppose you’re using Kali Linux and want to check for active connections on your system, focusing on TCP connections and identifying the processes associated with them. You can use the following command:
netstat -antp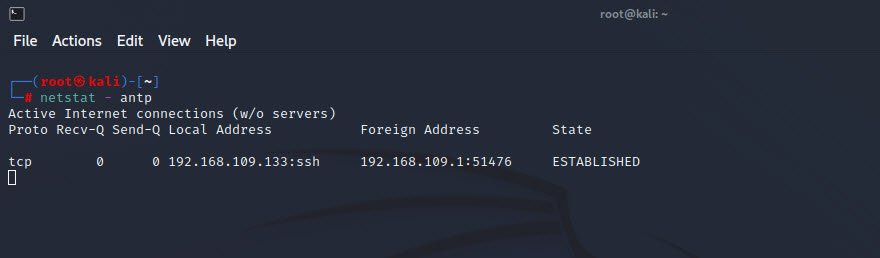
Executing this command will provide a comprehensive list of active TCP connections, along with the associated process information. You can use this information to identify any unexpected or suspicious network activities. For instance, if you notice a process you don’t recognize or a connection on an uncommon port, it could be an indicator of a security issue.
Example: Monitoring Apache Web Server
In your exploration of active connections with `netstat`, you may find it particularly useful for monitoring services like web servers.
For instance, if you’ve set up an Apache web server on your Kali Linux machine, running the `netstat` command might reveal something like this:
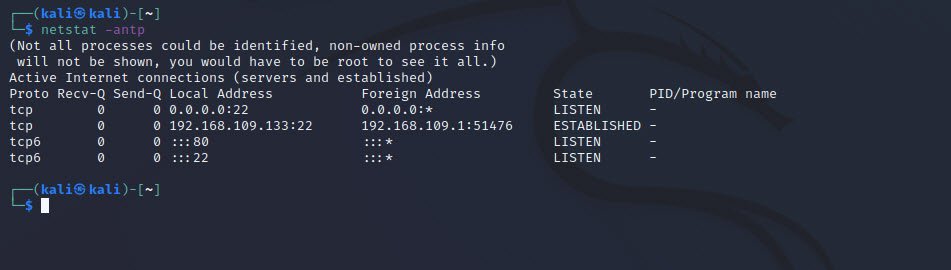
In this example, you can see that the system is listening on port 80, which is the default port for HTTP traffic.
To start or stop the Apache web server on Kali Linux, you can use the following commands:
# To start Apache
service apache2 start
# To stop Apache
service apache2 stopThese commands allow you to control the Apache service, which can be useful for troubleshooting or temporarily shutting down the web server.
Conclusion
`Netstat` is an indispensable tool in Kali Linux, providing valuable insights into active network connections and associated processes. By using its various options, such as `-a`, `-n`, `-t`, and `-p`, you can tailor your network monitoring to your specific needs, whether it’s identifying security threats, troubleshooting network issues, or simply gaining a better understanding of your system’s network activities.
In the ever-evolving landscape of cybersecurity, `netstat` remains a powerful ally in the arsenal of Kali Linux users.







This Post Has One Comment