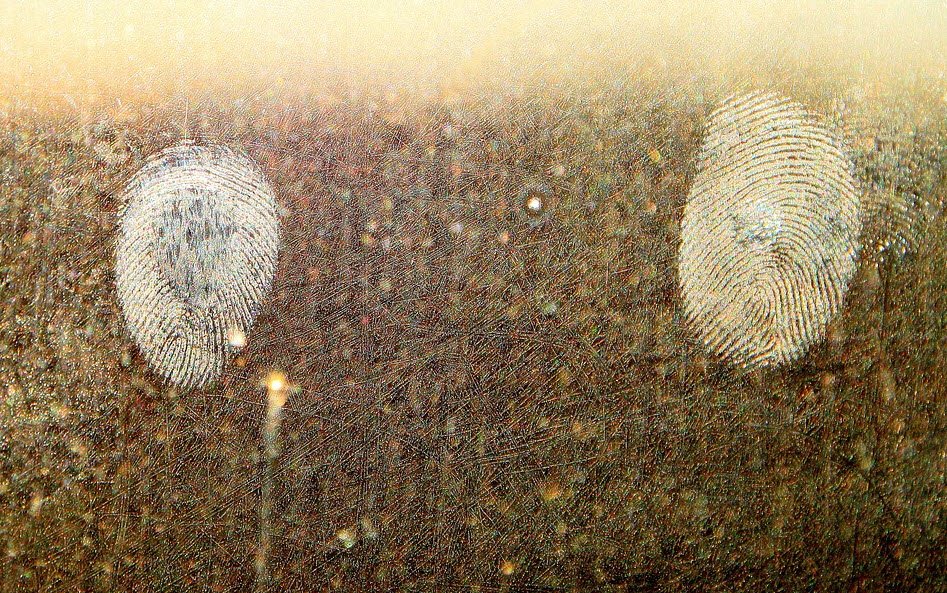
The field of computer investigations and forensics is still in its developing stages. The need for computer forensics has become more apparent with the exponential increase in the number of cyber crimes and…
Read more
In attempting to build a secure organization, where should you start? One commonly held belief is that you should initially identify your assets and allocate security resources based on the value of each…
Read more
In the modern era, information technology has facilitated transmission of multi-facet information across the world. Alexa Rank is a global and regional result of just how popular the site is. In other words,…
Read more
Hacking is an art or a technique which is used to find the solution for a typical problem by implementing either the legal or illegal ways. It may or may not be done…
Read more
Cryptography is a tool for protecting information in our computer systems. The art of protecting information by encrypting into an unreadable format, called as cipher text. Only those who possess a secret key…
Read more
Understanding the way people’s brains work would be the key to building the ultimate web applications. Web applications are applications whose functionality is processed on a web server, and is delivered to the…
Read more
This article offers you a solid foundation for the Certified Information Systems Security Professional (CISSP) exam. This article is designed for readers and students who want to study for the CISSP certification exam….
Read more
Having problems with your site not sending emails? Email has been a major part of the Internet revolution, and not just because it has streamlined the junk mail industry. When a message is…
Read more
A structure is a collection of related data items which can be of different types held together in a single unit. The data items enclosed within a structure are known as its members…
Read more
Well Known ports (also known as system ports) are numbered from 0 through 1023. In computer networking, the term port can refer to either physical or virtual connection points. Physical network ports allow…
Read more
Of all the communications services available today, wireless services are having the most dramatic impact on our personal and professional lives, enhancing personal productivity, mobility, and security. The wireless industry worldwide is experiencing…
Read more
This article offers you a solid foundation for the Certified Information Systems Security Professional (CISSP) exam. This article is designed for readers and students who want to study for the CISSP certification exam….
Read more
Computers and the Internet has become a very important part of our lives. It eases the tasks of our daily life in every way. Whenever we use the Internet for any purpose, we…
Read more