There are many coding patterns that are useful for system design interviews. Some of the most common patterns include:
- Singleton pattern: This pattern ensures that there is only one instance of a class in an application. This is useful for classes that represent resources that should only be accessed by one thread at a time, such as database connections.
- Factory pattern: This pattern creates objects without exposing the instantiation logic to the client. This can be useful for creating objects that have different implementations, such as different types of database connections.
- Builder pattern: This pattern breaks down the construction of a complex object into a series of steps. This can be useful for creating objects that have a lot of dependencies, such as a web application.
- Decorator pattern: This pattern allows you to add new functionality to an object without modifying the object’s original code. This can be useful for adding logging or security features to an object.
- Adapter pattern: This pattern allows you to make two incompatible interfaces compatible with each other. This can be useful for integrating legacy systems with new systems.
These are just a few of the many coding patterns that are useful for system design interviews. By understanding these patterns, you can design systems that are more efficient, scalable, and maintainable.
Here are some examples of how these patterns can be applied in system design interviews:
- The singleton pattern can be used to ensure that there is only one instance of a database connection object in an application. This can prevent race conditions and other errors that can occur when multiple threads try to access the same database connection at the same time.
- The factory pattern can be used to create different types of database connections, such as MySQL connections, PostgreSQL connections, and Oracle connections. This can make it easier to switch between different database systems in the future.
- The builder pattern can be used to create complex objects, such as a web application. This can make it easier to keep track of the different parts of the application and to make changes to the application in the future.
- The decorator pattern can be used to add logging or security features to an object. This can make it easier to track the behavior of the object and to protect the object from unauthorized access.
- The adapter pattern can be used to integrate legacy systems with new systems. This can make it easier to migrate data from legacy systems to new systems and to use the features of new systems with legacy systems.
By understanding these patterns, you can design systems that are more efficient, scalable, and maintainable.
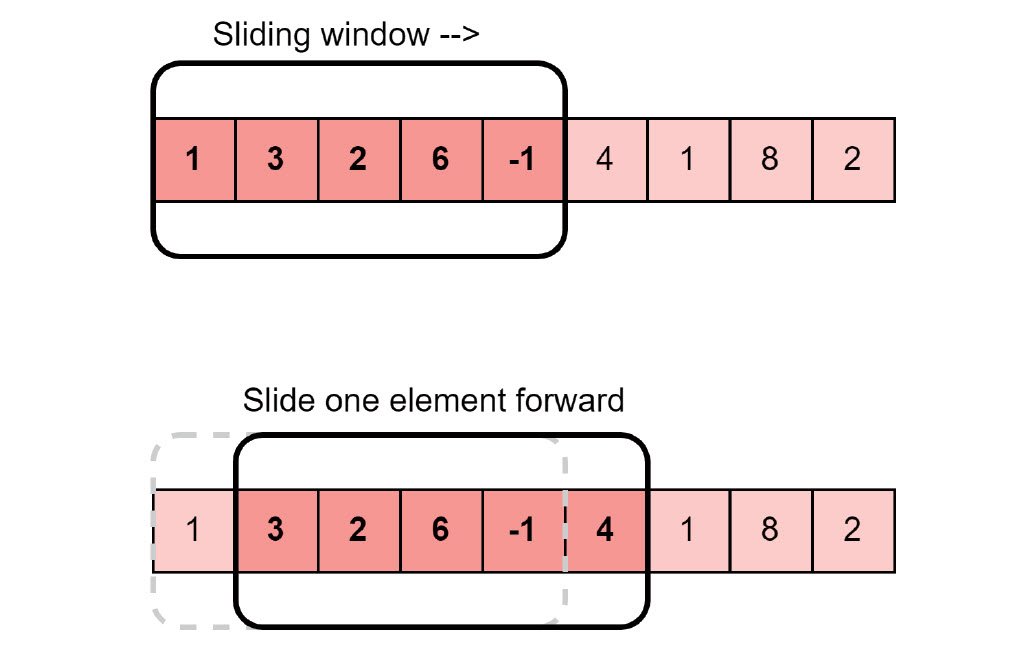
1. Sliding Window
Maintains a “window” of elements in a data structure (usually an array or a string) to optimize the solution of a problem.
Usage:
- Network congestion control algorithms (like TCP)
- Data compression algorithms (like LZ77)
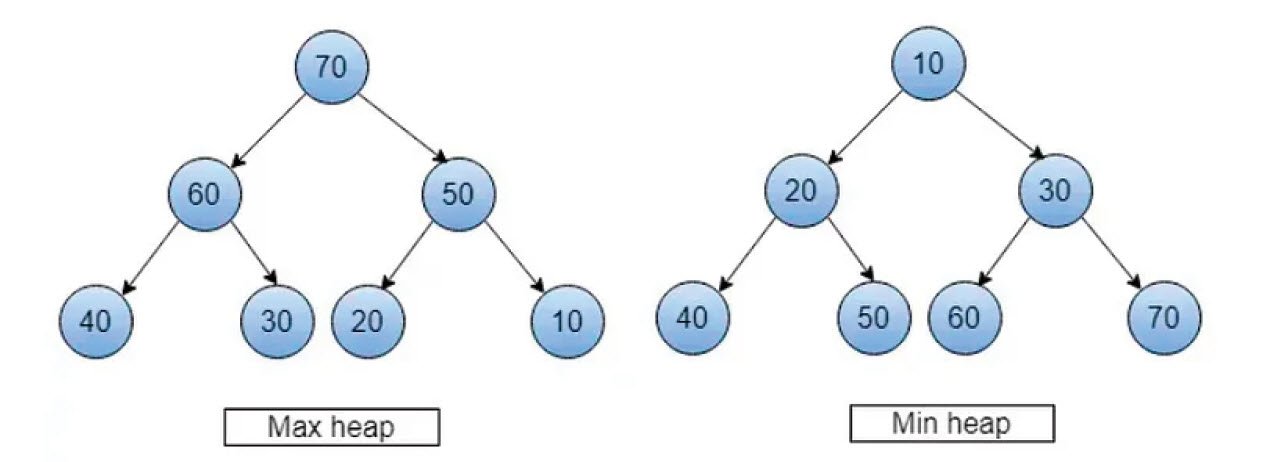
2. Two Heaps
Uses two heaps (min-heap and max-heap) to maintain a specific order of elements to efficiently solve problems.
Usage:
- Managing a priority queue in a schedule.
- Implementing Dijkstra’s shortest path algorithm.
- Maintaining the median of a dynamic data set.
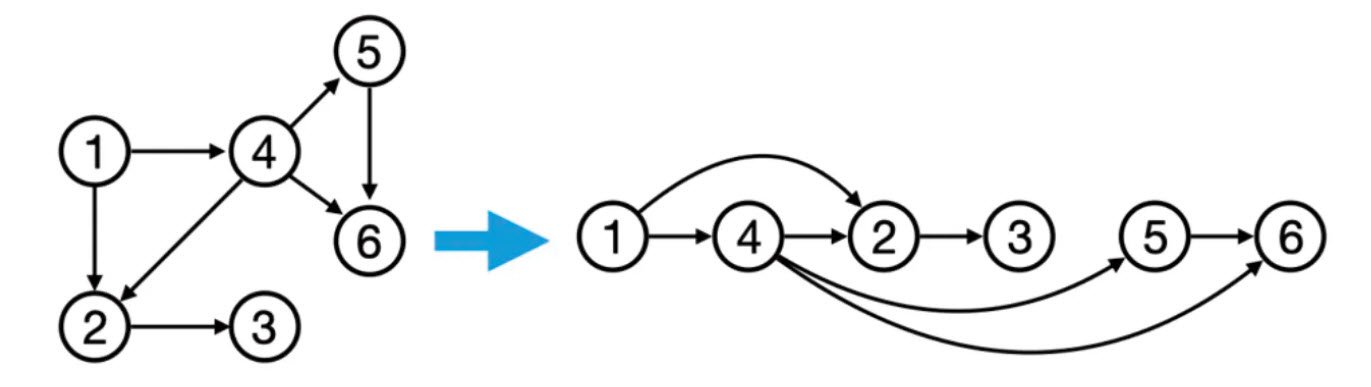
3. Topological Sort
Used for linear ordering of the vertices of a directed acyclic graph (DAG) such that for every directed edge (u, v), vertex u comes before vertex v in the ordering.
Usage:
- Scheduling tasks with dependencies.
- Determining the order of compilation for a set of source files.
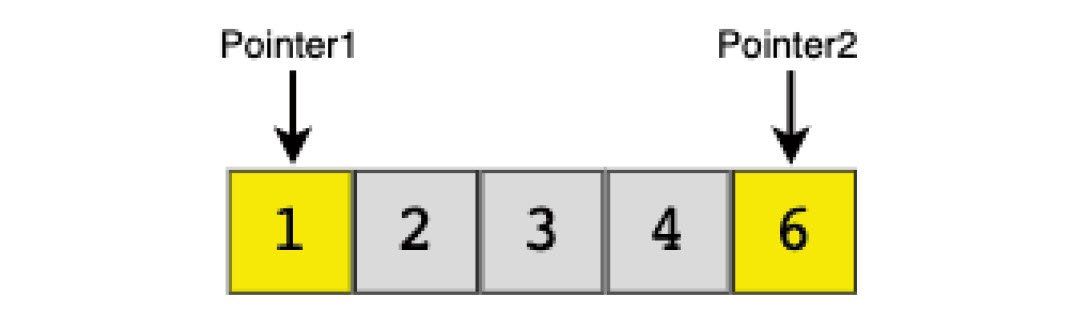
4. Two Pointers
Uses two pointers that move through the data structure (often an array) in a coordinated manner to solve problems.
Usage:
- Merge-sort algorithm.
- Binary search.
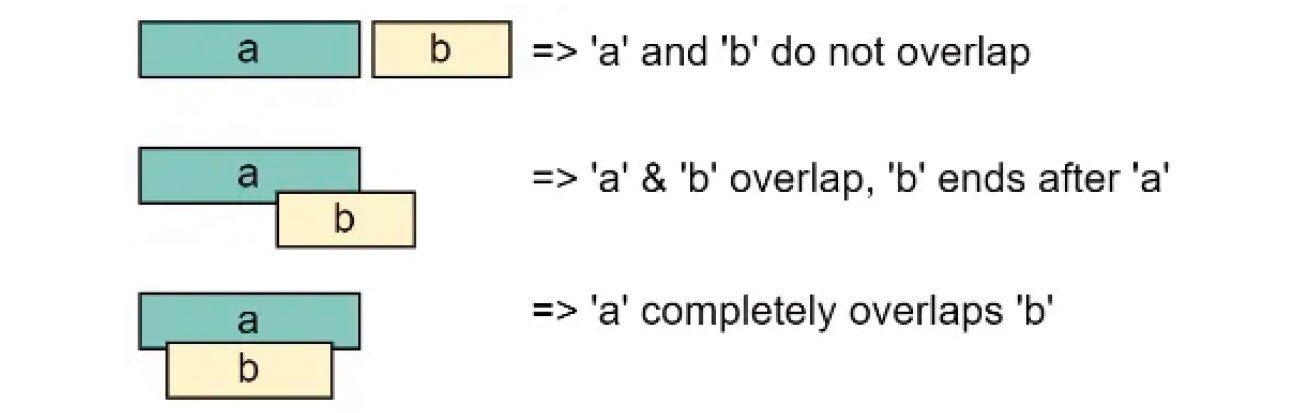
5. Merge Intervals
Involves merging of overlapping or continuous intervals in a given data structure (usually an array or a list) to optimize solutions for a specific problem.
Usage:
- Scheduling meeting rooms.
- Managing calendar events.
- Optimizing resource allocation.
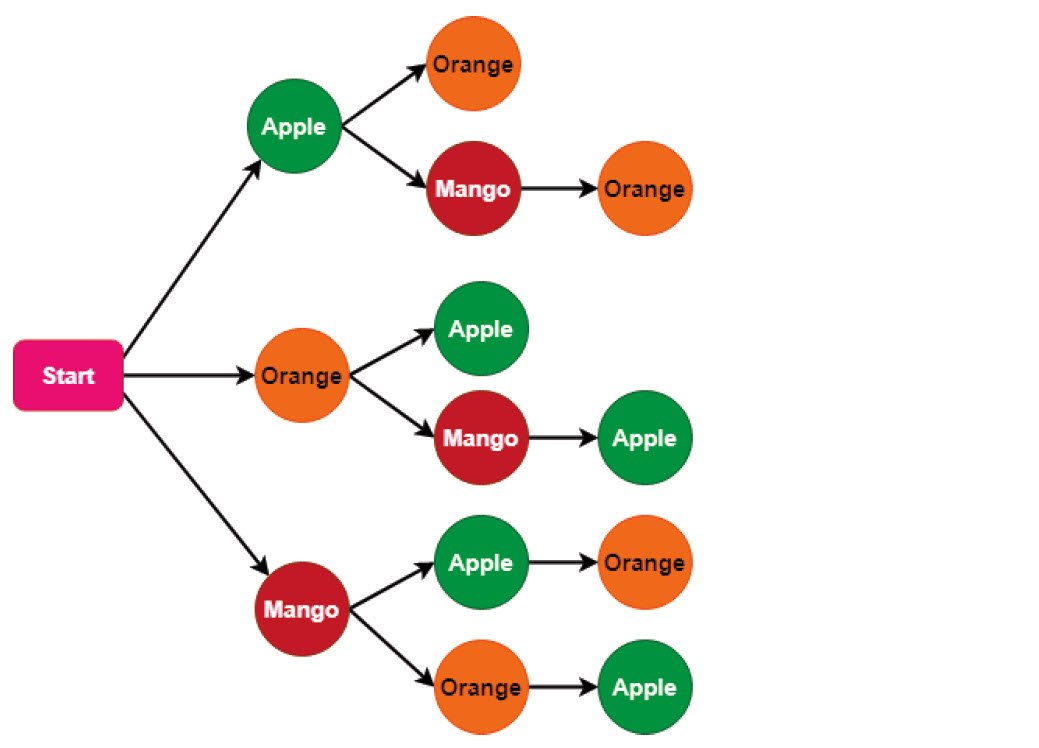
6. Backtracking
Tries out different possibilities, undoing them, and then trying out new paths until a solution is found.
Usage:
- Solving Sudoku puzzles.
- Generating permutations and combinations.
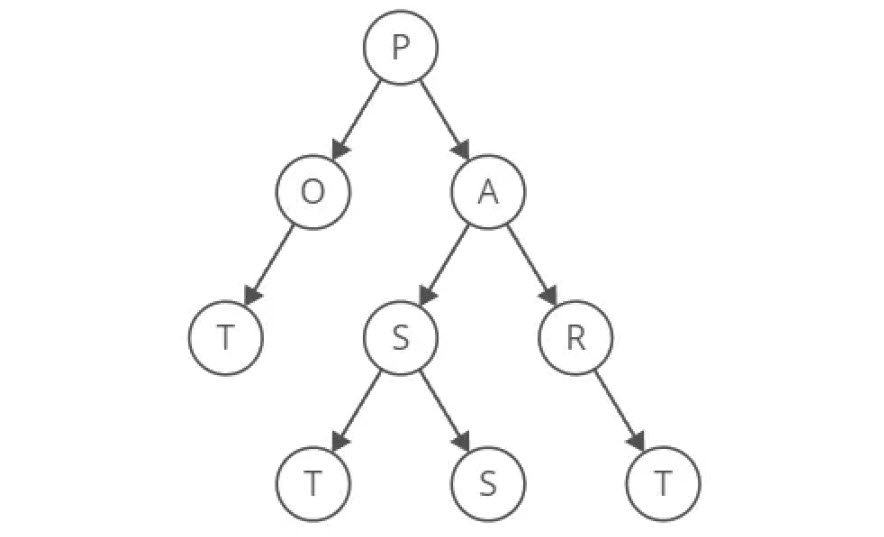
7. Trie (Prefix Tree)
Uses a tree-like data structure to efficiently store and retrieve strings based on their prefixes.
Usage:
- Implementing an autocomplete system.
- Spell checkers.
- IP routing (Longest Prefix Matching).
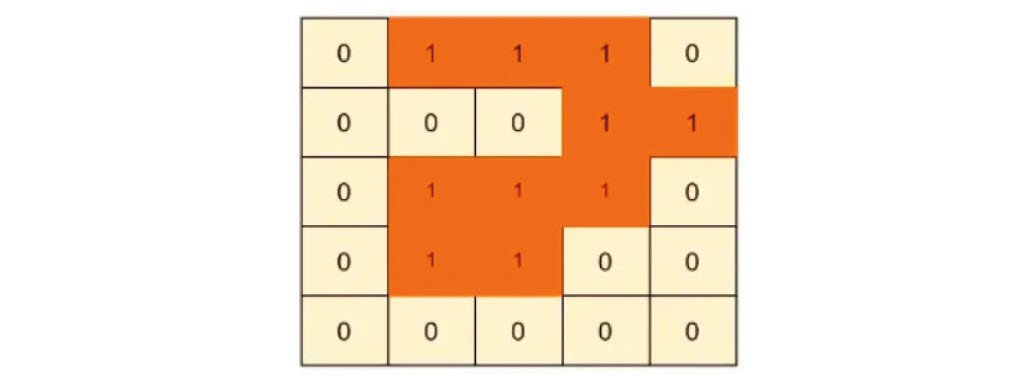
8. Flood Fill
Traverses a 2D grid (matrix) and replacing connected elements of a specific value with a new value.
Usage:
- Filling a bounded area in graphics editors (like MS Paint).
- Counting connected regions in a 2D grid.
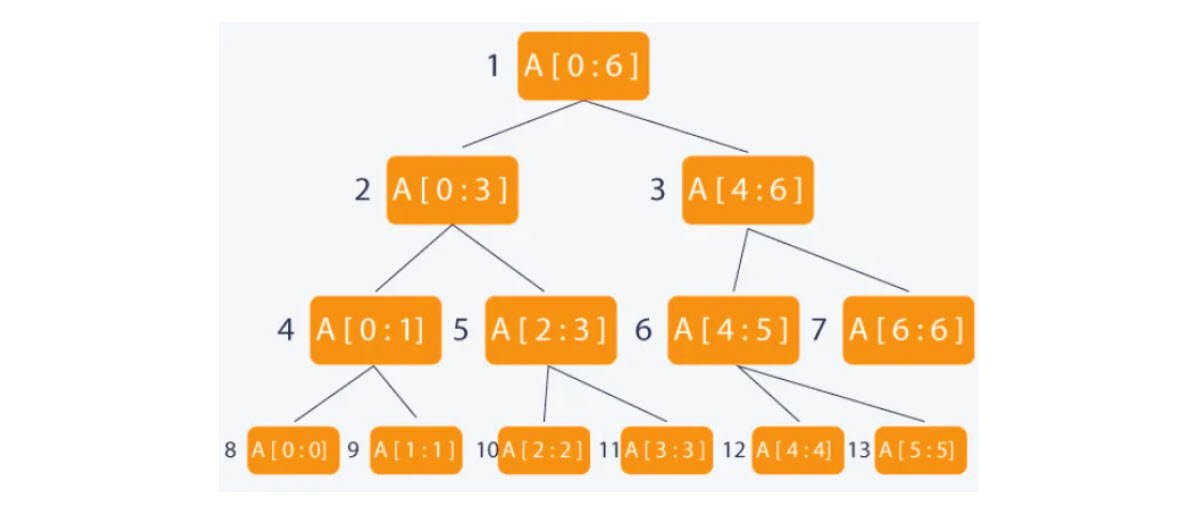
9. Segment Tree
Uses a tree-like data structure to efficiently perform range queries and updates on an array or a list.
Usage:
- Range queries in databases.
- Calculating range-based statistics (e.g., minimum, maximum, sum).
10. Breadth-First Search (BFS)
Traverses a tree or a graph using a breadth-first approach, visiting all nodes at the current level before moving to the next level.
Usage:
- Web crawlers.
- Social network analysis (finding friends of friends) Routing algorithms (like OSPF) in networking.
11. Depth-First Search (DFS)
Traverses a tree or a graph using a depth-first approach, visiting a node and exploring as far as possible along a branch before backtracking.
Usage:
- Solving mazes.
- Finding connected components in a graph.
- Generating permutations or combinations.
12. Union-Find (Disjoint Set)
Uses a data structure to keep track of disjoint sets and efficiently perform union and find operations on them.
Usage:
- Network connectivity
- Finding connected components in a graph
- Top 10 CSS Libraries for Your Next App
- How To Fix the Crowdstrike/BSOD Issue in Microsoft Windows
- MICROSOFT is Down Worldwide – Read Full Story
- Windows Showing Blue Screen Of Death Error? Here’s How You Can Fix It
- A Guide to SQL Operations: Selecting, Inserting, Updating, Deleting, Grouping, Ordering, Joining, and Using UNION
- Top 10 Most Common Software Vulnerabilities
- Essential Log Types for Effective SIEM Deployment
- How to Fix the VMware Workstation Error: “Unable to open kernel device ‘.\VMCIDev\VMX'”
- Top 3 Process Monitoring Tools for Malware Analysis
- CVE-2024-6387 – Critical OpenSSH Unauthenticated RCE Flaw ‘regreSSHion’ Exposes Millions of Linux Systems