Securing your web server is a crucial aspect of maintaining a robust online presence. One of the steps to enhance security is to disable unnecessary and potentially insecure HTTP methods. Apache, one of the most widely used web servers, allows users to achieve this by leveraging the mod_rewrite module.
In this article, we will guide you through the process of disabling the HTTP OPTIONS method in Apache, and the same steps can be applied to disable other methods like HEAD, PUT, and DELETE.
Step 1: Open .htaccess File
Firstly, make sure that the mod_rewrite module is enabled on your Apache web server. This can typically be done by locating and editing the `.htaccess` file, commonly found in the root directory of your web server, often at `/var/www/html/.htaccess`.
You can use a text editor to open the file. In this example, we’ll use the `nano` editor:
sudo nano /var/www/html/.htaccessStep 2: Disable HTTP OPTIONS Methods
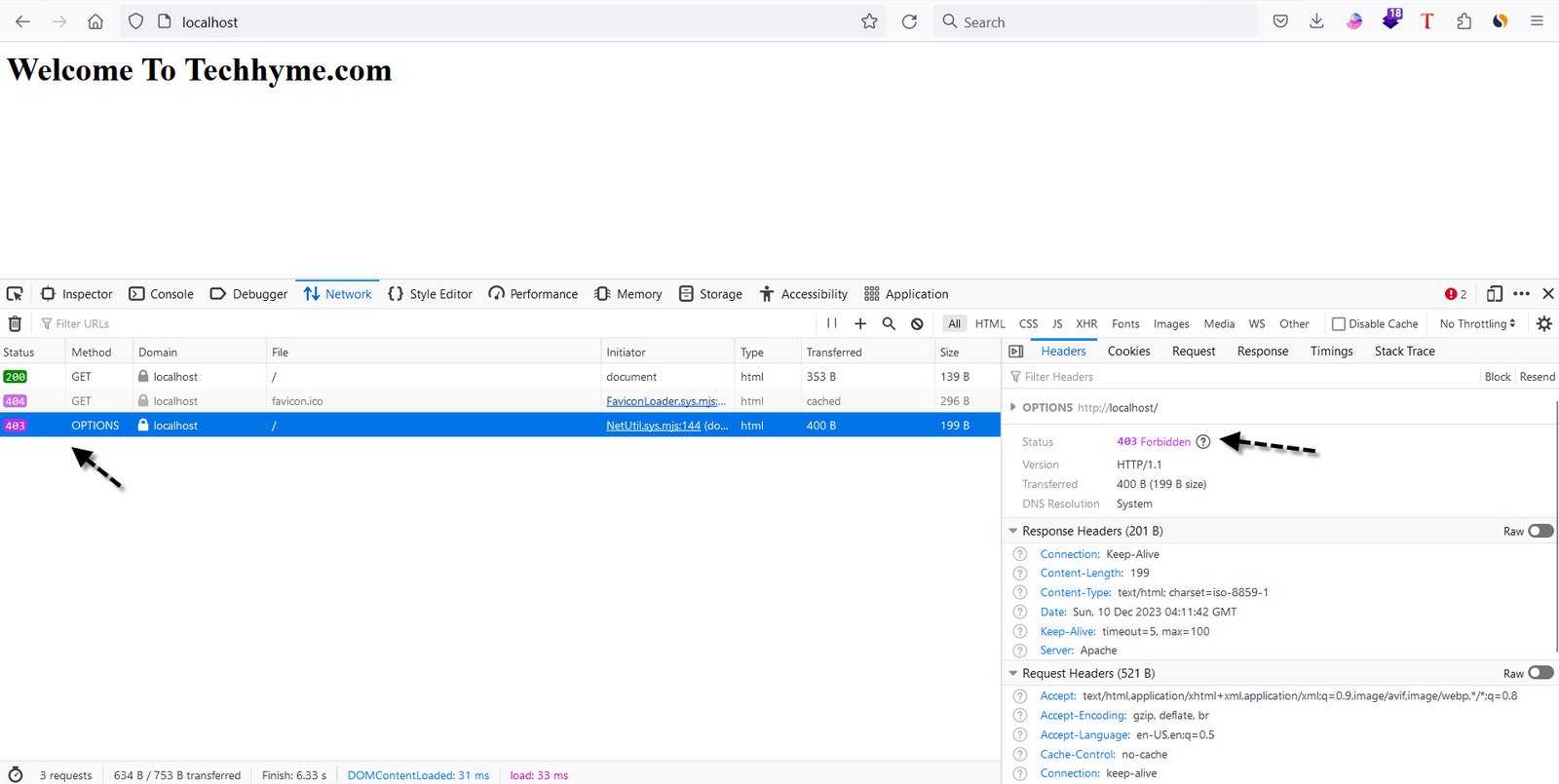
To disable the HTTP OPTIONS method, add the following lines to your `.htaccess` file:
RewriteEngine On
RewriteCond %{REQUEST_METHOD} ^(TRACE|TRACK|OPTIONS)
RewriteRule .* - [F]Explanation of the code:
- The first line activates the mod_rewrite module.
- The second line checks if the request method is OPTIONS, TRACE, or TRACK.
- The third line forbids access (`[F]`) to requests with these methods.
To disable other methods such as HEAD, PUT, and DELETE, modify the second line accordingly. For example, to disable HEAD, PUT, and DELETE:
RewriteEngine On
RewriteCond %{REQUEST_METHOD} ^(HEAD|PUT|DELETE)
RewriteRule .* - [F]Step 3: Restart Apache Web Server
Once you have made the necessary changes, restart the Apache web server to apply the configuration:
sudo service apache2 restartThese steps should effectively disable the specified HTTP methods and enhance the security of your Apache web server.
By following these guidelines, you can significantly reduce the attack surface of your web server and minimize the risk of potential security vulnerabilities. Always ensure that you have a backup of your configuration files before making changes and regularly review and update your server security practices.
You may also like:- How To Install Python 2.7.18 From The Source
- How To Parse SSH Authentication Logs with Logstash
- How To Easily Crack Wi-Fi Password
- 6 Most Useful Windows Command Prompt Commands
- Ripgrep – Searching for Specific File Types and Beyond
- Insert and Create Data in Elasticsearch
- Manage Time and Date in Linux with timedatectl
- How to Set Network Adapter Priority on Windows 11
- How to Add a User to Sudoers on Ubuntu
- 25 Popular Linux IP Command Examples