
SQL injection is a pervasive and potentially devastating form of cyber attack, where malicious actors exploit vulnerabilities in a web application’s code to execute arbitrary SQL code. This unauthorized access allows attackers to…
Read more
SQL injection (SQLi) is a prevalent security vulnerability that can have severe consequences if exploited by attackers. Testing for SQL injection vulnerabilities is crucial to identifying and mitigating potential risks to web applications….
Read more
SQL injection (SQLi) is a prevalent and dangerous attack vector that exploits vulnerabilities in a web application’s database layer. Attackers manipulate input fields to inject malicious SQL queries into an application’s database, potentially…
Read more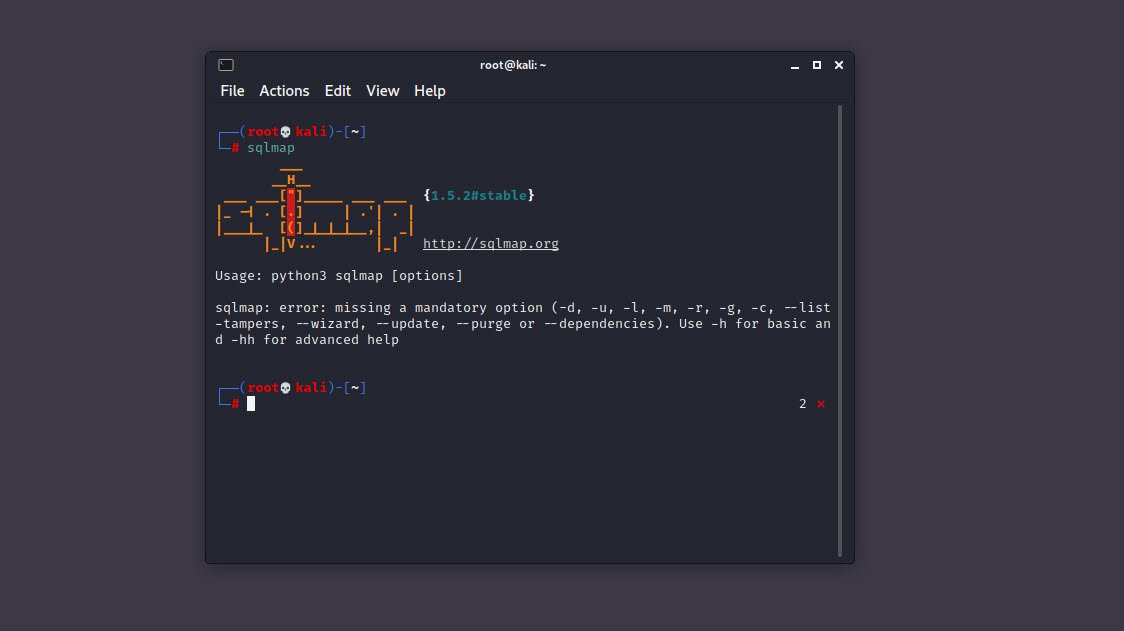
Structured Query Language, which is better known as SQL, is the underlining common programming language that is understood by most database management systems. It provides a common way for application to access the…
Read more