MobSF stands for Mobile Security Framework. It is an open-source, automated mobile application security testing tool that helps developers, security researchers, and testers to identify security vulnerabilities in mobile applications.
MobSF supports both Android and iOS platforms and can perform a variety of security tests, including static analysis, dynamic analysis, and malware analysis. Some of the security tests that MobSF can perform include finding sensitive information in the app, detecting insecure data storage, identifying code vulnerabilities, checking for insecure communication, and more.
Some of the key features of the MobSF dashboard include:
- Real-time status updates on the analysis progress and results.
- Detailed reports on the application’s components, permissions, and vulnerabilities.
- A graphical overview of the security issues detected by the tool.
- The ability to drill down into specific issues and view detailed information about them.
- Customizable charts and graphs that can help you visualize trends and patterns in the security analysis results.
- A flexible filter system that allows you to focus on specific types of vulnerabilities or severity levels.
MobSF is a powerful tool that can help ensure the security of mobile applications and prevent security breaches.
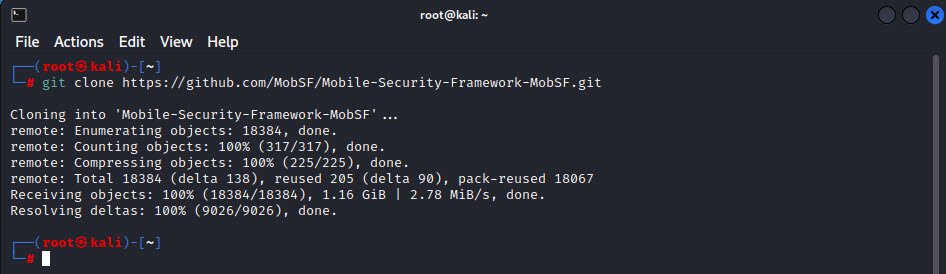
The first step is to download the package of MobSF from GitHub repository.
Command: git clone https://github.com/MobSF/Mobile-Security-Framework-MobSF.git
Navigate to the directory of MobSF and run the following command to install the setup.
Command: cd Mobile-Security-Framework-MobSF
Command: ./setup.sh
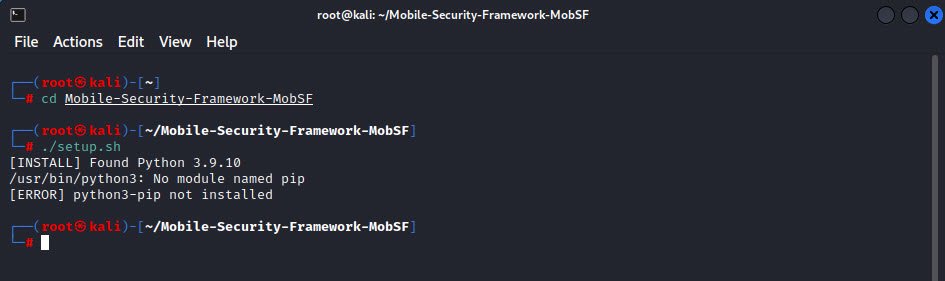
So as you can see that the “python3-pip” module is not installed in your system.
“python3-pip not installed” is an error message that typically appears when attempting to run a Python package installation command using pip on a system where pip is not installed or is not installed correctly.
Pip is the default package manager for Python and is used to install, manage, and update Python packages. If pip is not installed or not installed correctly, it will prevent you from using it to install packages.
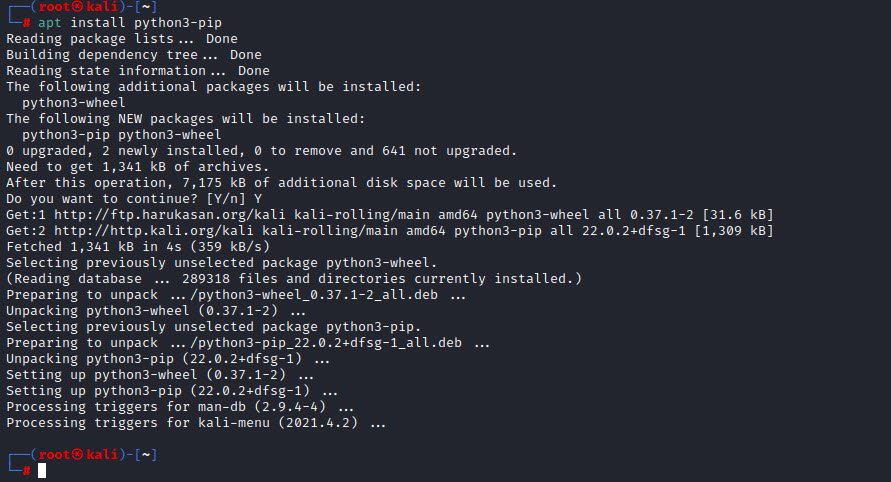
To resolve this error, you can try installing pip using your system’s package manager. For example, on Debian-based systems, you can run the following command to install pip for Python 3:
Command: apt install python3-pip
Now again run ./setup.sh command.
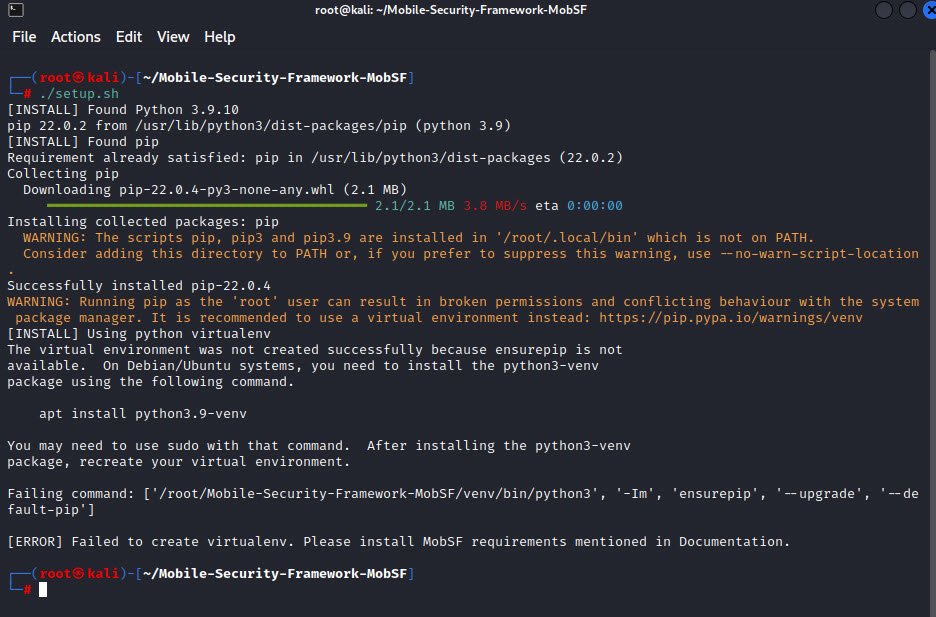
You also need to install the following package which is a virtual environment module:
Command: apt install python3.9-venv
A virtual environment is a self-contained Python environment that allows you to install packages and manage dependencies for a specific project or application, without affecting the global Python installation or other projects.
Python 3.9 venv module provides a lightweight and convenient way to create and manage virtual environments.
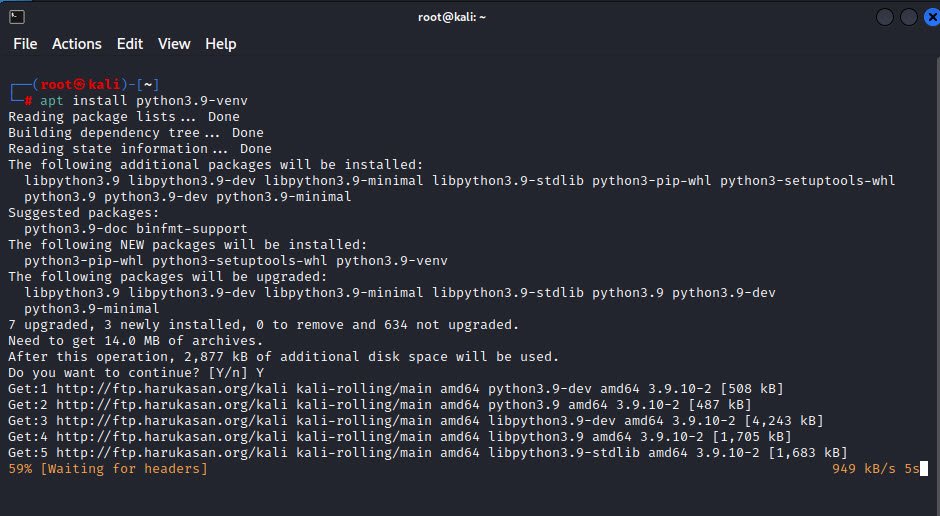
After successful installation of python virtual environment package, you will see the successful message at the end.

Now shoot below command to run MobSF.
Command: ./run.sh 127.0.0.1:8000
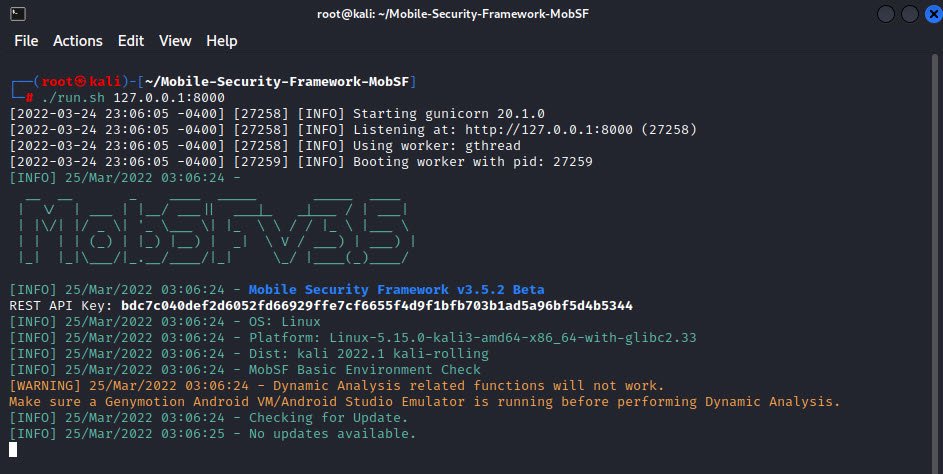
Now, you can easily access MobSF by browsing http://localhost:8000/
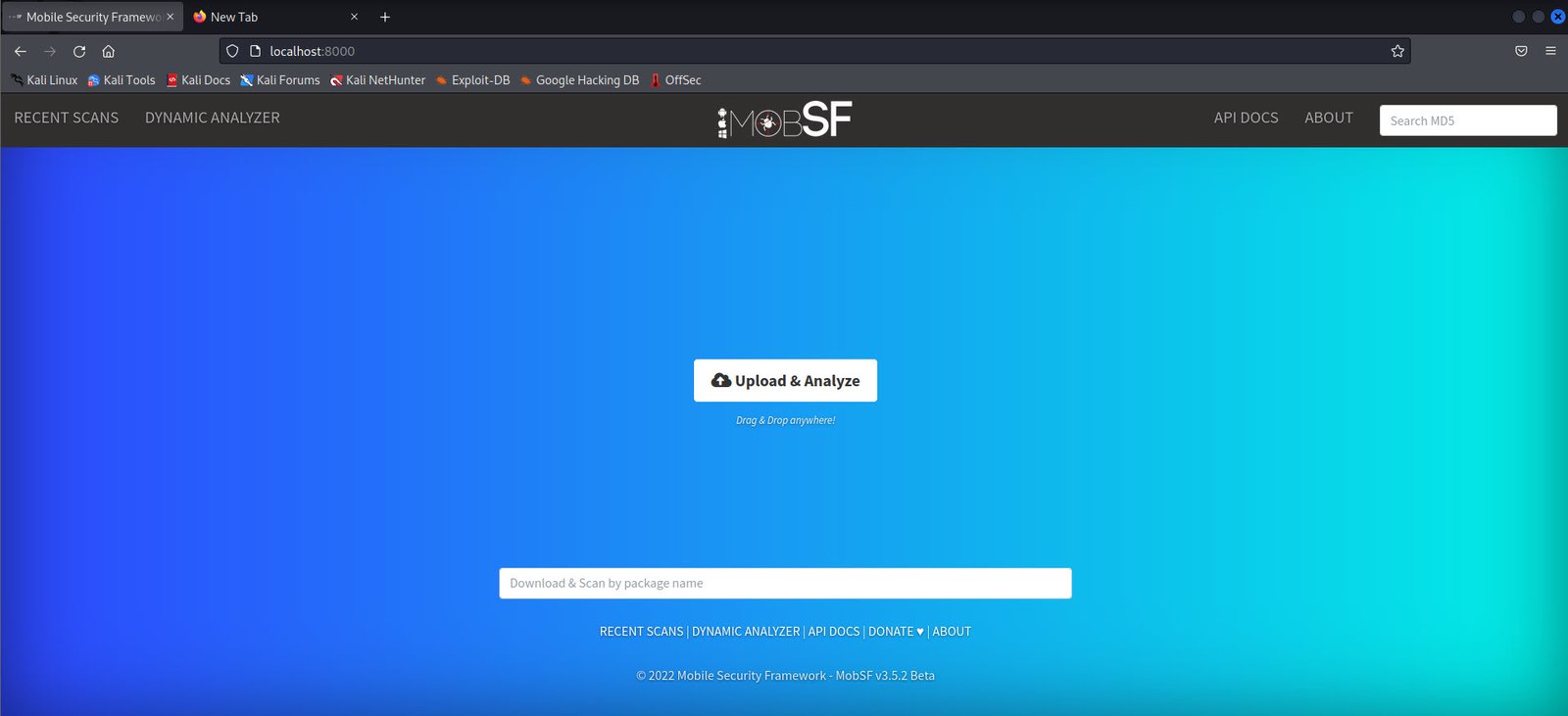
This should take you to the MobSF web interface, where you can start using the tool to perform security testing on your mobile applications.
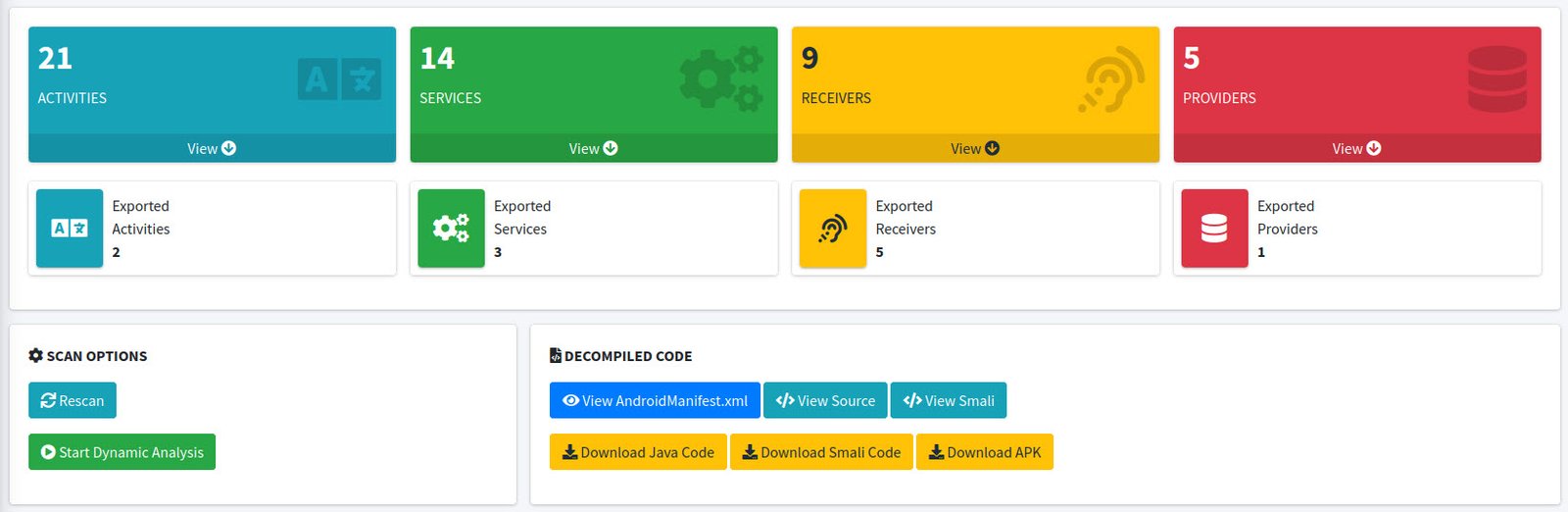
The dashboard provides a variety of tools and features for analyzing and managing security issues, including the ability to view detailed reports, generate charts and graphs, and filter results by severity or type of vulnerability.
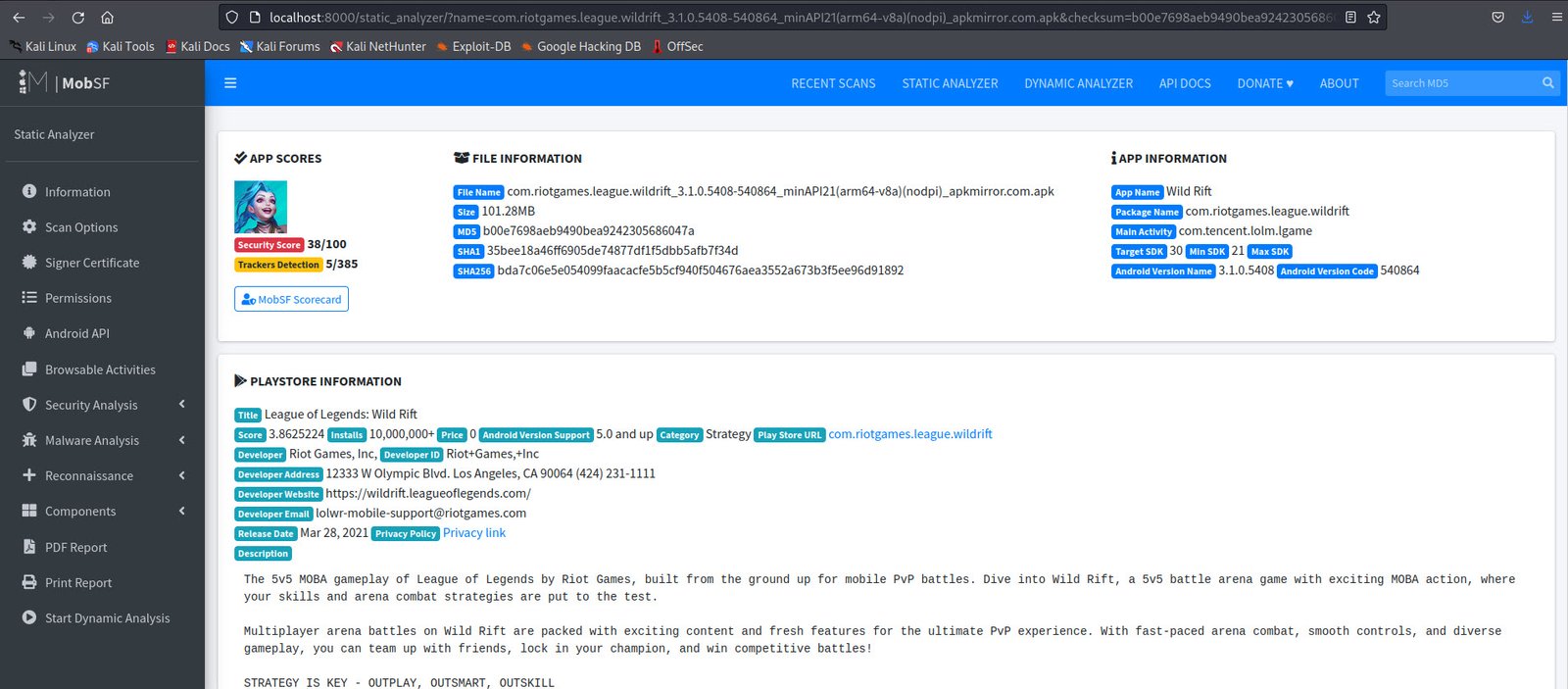
When you upload an APK file to MobSF, the tool automatically extracts and analyzes the modules requested by the application.
The permission analysis performed by MobSF can help you identify potential security issues in the application. For example, if the application requests sensitive permissions, such as access to the device’s camera or microphone, you may want to investigate why the application needs these permissions and ensure that they are being used appropriately.
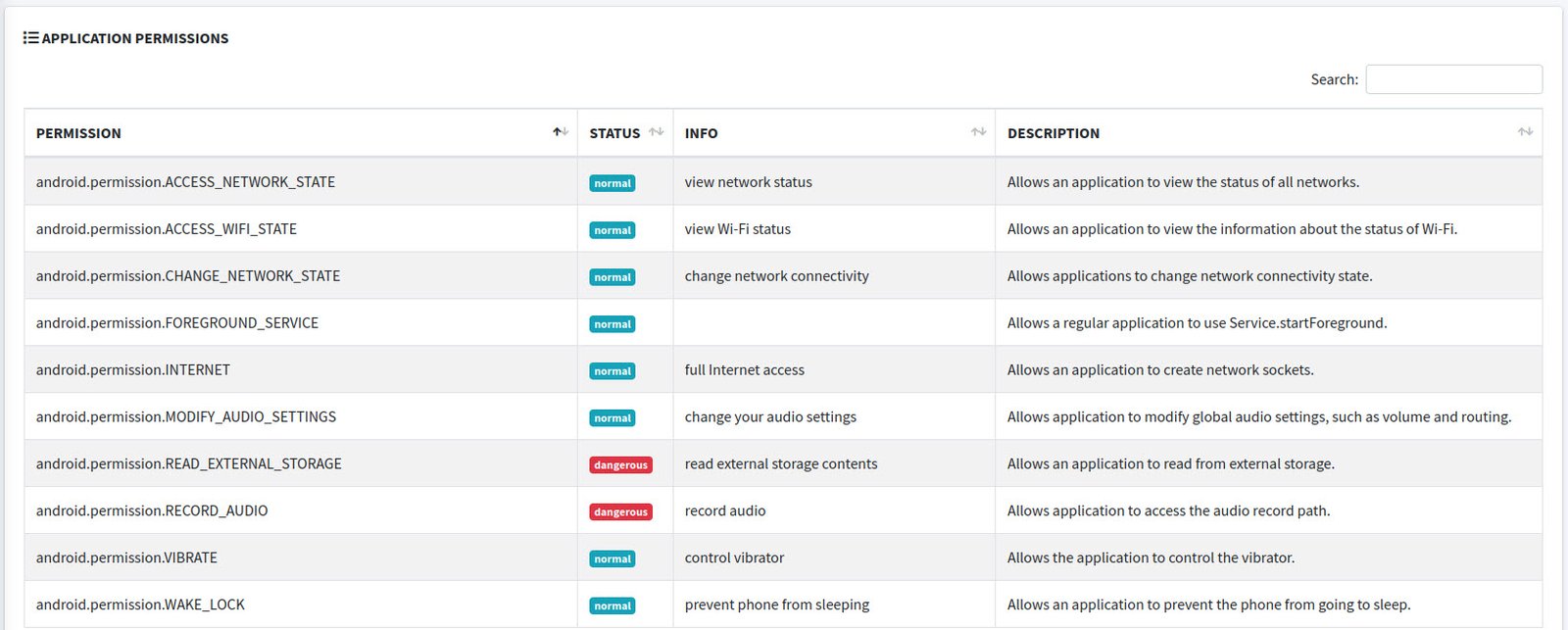
Overall, the MobSF dashboard is a powerful tool that can help developers, security researchers, and testers to identify and remediate security issues in mobile applications.
You may also like:- How To Install Python 2.7.18 From The Source
- How To Parse SSH Authentication Logs with Logstash
- A Comprehensive Guide to File System Commands in Linux
- Essential File Compression Commands in Linux
- Secure Shell (SSH) Protocol – A Comprehensive Guide
- Monitoring Active Connections in Kali Linux Using Netstat
- How To Easily Crack Wi-Fi Password
- 6 Most Useful Windows Command Prompt Commands
- Ripgrep – Searching for Specific File Types and Beyond
- Insert and Create Data in Elasticsearch