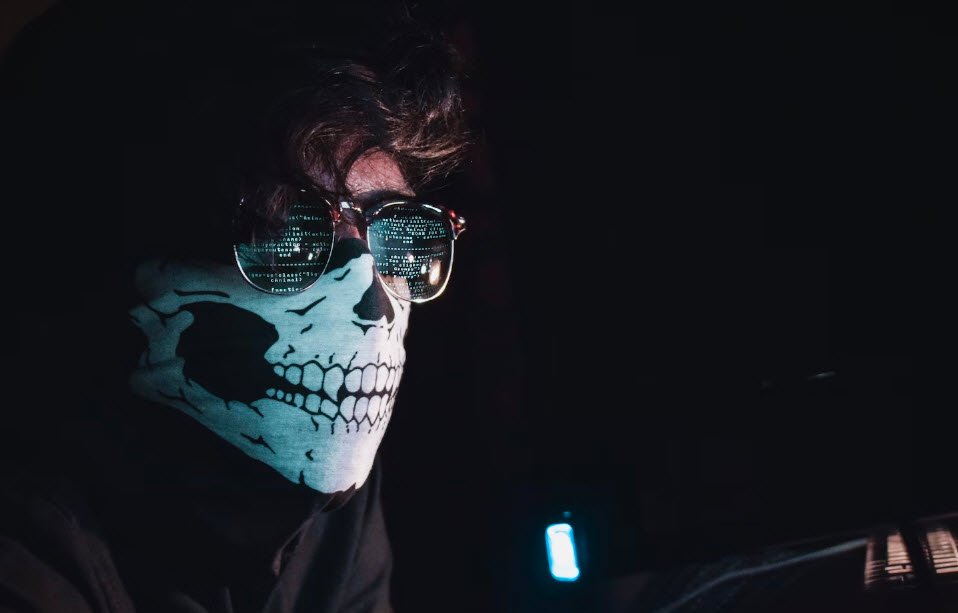
It is very tough being an IT professional or Cyber Security Expert in today’s world. The pace at which technology is advancing makes current perimeter security solutions look like sieves. Keeping up with the ever increasing number of new threats may seem like the best approach, but it might actually be a better idea to just slow down instead.
Most people assume that the biggest threats to cyber security will be posed by new or unknown vulnerabilities. However, experts agree that, in fact, these threats will emanate from well-known weaknesses. These vulnerabilities are linked to some of the current technologies that are gaining more acceptance, popularity, and use all over the world.
Some of these current technological trends that form the future of hacking include:
Cloud Computing
As more organizations and businesses take to the cloud, hackers too are shifting their attention to attacking cloud computing platforms. There is an increase in demand for methods like penetration testing to be used to identify cloud computing threats before they happen. Businesses are also seeking development of countermeasures to prevent such attacks.
The challenge that hacking security teams face with cloud apps is their limited visibility and few control options. It is understood that the cyber attacks of the future will occur within what is known as “Shadow Data/IT.” This is data or IT activities that take place on a cloud without being monitored, controlled, or secured. Shadow Data/IT results in the creation of new threat vectors, including misuse and ultimate leakage of data, and allowing malicious hackers easy access to a system or network.
In order for organizations and businesses to deal with Shadow Data/IT, they will have to formulate corporate strategies that require employees to change the way they use data on a cloud. There will have to be some kind of shift in culture, from detection and punishment to acceptance and protection.
It is going to be difficult for organizations to regulate employees’ cloud activities, but they may not have to go to such extremes. There should at least be technology for monitoring Shadow Data/IT on different cloud services so that visibility allows for reduction of risks.
Mobile Devices and Platforms
Today, almost every system or application can be accessed via any mobile device, platform, or browser. This has resulted in hackers shifting their attention to these new targets. There has been a surge in the popularity of mobile hacking tools in recent years.
New Vulnerabilities
Malicious hackers never tire looking for new vulnerabilities to exploit and crack into networks. Examples of new vulnerabilities include:
- Heart bleed CVE-2014-0160
- Shellshock CVE-2014-6271
- Poodle CVE-2014-3566
Career Opportunities for Hackers
With all the threats rising up in today’s advancing digital world, there is concern that malicious hackers can attack whenever and wherever they please. This means that the best solution is to employ ethical hackers to constantly scout for weak links and develop appropriate countermeasures.
This is the work of an ethical hacker.
Demand is growing daily for ethical hacking professionals, whether it’s from governments or commercial enterprises.
Anyone aspiring to be an ethical hacker needs to consider getting certified and becoming a professional – a Certified Ethical Hacker (CEH).
The pay is good, averaging $20,000 to $40,000 for every assignment. The client environment also plays a role in remuneration.
The latest edition of the ethical hacking certification is CEH v12. Some of the requirements include IT experience, basic knowledge of Linux/UNIX, and a good understanding of TCP/IP. This is definitely something to consider if you want to make a career out of hacking.
You may also like:- How To Fix the Crowdstrike/BSOD Issue in Microsoft Windows
- MICROSOFT is Down Worldwide – Read Full Story
- Windows Showing Blue Screen Of Death Error? Here’s How You Can Fix It
- A Guide to SQL Operations: Selecting, Inserting, Updating, Deleting, Grouping, Ordering, Joining, and Using UNION
- Top 10 Most Common Software Vulnerabilities
- Essential Log Types for Effective SIEM Deployment
- How to Fix the VMware Workstation Error: “Unable to open kernel device ‘.\VMCIDev\VMX'”
- Top 3 Process Monitoring Tools for Malware Analysis
- CVE-2024-6387 – Critical OpenSSH Unauthenticated RCE Flaw ‘regreSSHion’ Exposes Millions of Linux Systems
- 22 Most Widely Used Testing Tools








