
In an era marked by rapid technological advancement, cybersecurity has become an increasingly critical concern. With cyber threats evolving at an alarming rate, staying updated with the latest strategies and insights is essential…
Read more
In the realm of cybersecurity and digital investigations, information gathering is a critical phase that lays the foundation for understanding potential threats, assessing vulnerabilities, and making informed decisions. Whether you’re a security professional,…
Read more
In the world of cybersecurity, having the right certification can make a significant difference. It not only enhances your credibility but also ensures that you have the necessary skills to protect systems against…
Read more
SQL injection is a type of cyberattack where malicious actors exploit vulnerabilities in a web application’s code to gain unauthorized access to a database. While ethical hacking and penetration testing have legitimate use…
Read more
Security Information and Event Management (SIEM) systems play a crucial role in protecting organizations against cyber threats by collecting, analyzing, and correlating security event data from various sources. SIEM solutions are capable of…
Read more
Ethical hacking is an important skill in today’s digital age, where cyber attacks are becoming more common. Here are nine basic skills that you should have to become an ethical hacker in 2023:…
Read more
With the rise of cybersecurity threats and attacks, the need for skilled professionals to identify and fix vulnerabilities has become increasingly important. This has given rise to the field of ethical hacking, a…
Read more
There’s no way that you can start an ethical hacking process without first planning your security testing. There needs to be a clear agreement on the tactical and strategic issues involved in the…
Read more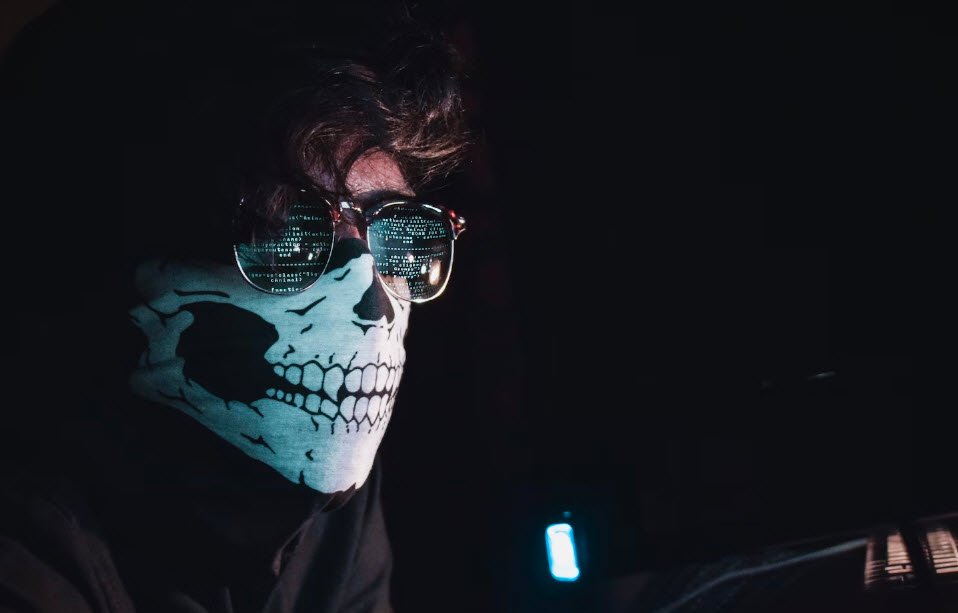
It is very tough being an IT professional or Cyber Security Expert in today’s world. The pace at which technology is advancing makes current perimeter security solutions look like sieves. Keeping up with…
Read more
Hacking is an art or a technique which is used to find the solution for a typical problem by implementing either the legal or illegal ways. It may or may not be done…
Read more